The FBI’s cybersecurity site was breached, resulting in the exposure of thousands of users’ personal information on a dark web forum frequented by cybercriminals.
It is believed that the personal information of over 80,000 users of the InfraGard portal has been compromised, with hackers sending members direct messages from an account pretending to be an FBI-vetted CEO in the financial sector.
InfraGard collaborates with companies to disseminate data on cyberattacks and other security risks.
Photo op with the CEO
This group’s members’ names and email addresses were listed for sale on Breached, a new cybercrime forum.
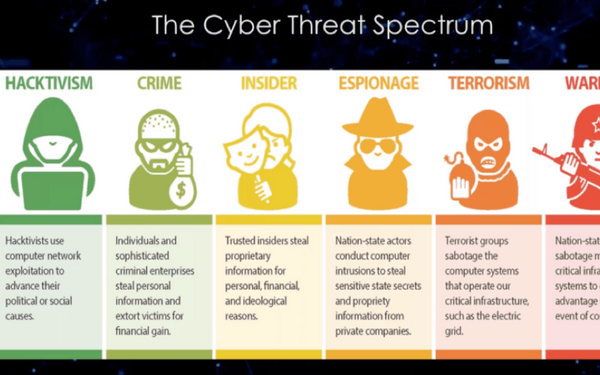
Members of InfraGard have been vetted by the organisation. These members are the top brass of cybersecurity firms that have been tasked with protecting critical infrastructure. The FBI and businesses will share information in an effort to raise awareness of cybersecurity risks.
“This is an ongoing case, and we are not able to give any details at this time,” the FBI said in response.
The vendor of Breached contacted KrebsOnSecurity and said they had filed for an InfraGard account while posing as the legitimate CEO of a large credit rating company.
They filled out the application using their own name, SSN, email address (which they claimed to have hacked), and phone number. According to the genuine CEO, who spoke with KrebsOnSecurity, the FBI never contacted them about the application.
Hacker got communication from InfraGard in early December confirming acceptance, something they had not expected.
Multi-factor authentication is required to access InfraGard, although customers have the option of having their one-time code emailed to them rather than sent through SMS. The hacker said that the plan would have failed if they had been restricted to using only phones, as they had dialled the CEO’s actual number.
They claimed they just used an API in the portal’s member-to-member communication features to take the database. They ran a Python script against it to extract the information, which included details on each user.
The hacker indicated that their true intention was to continue masquerading as a CEO and make contact with additional InfraGard members, maybe in an effort to collect even more sensitive information.
Pompompurin, the forum moderator for Breached, has a past with the FBI. Last year, they used a loophole in a different gateway for exchanging data between the FBI and local law enforcement to send massive volumes of spam from what appeared to be official FBI accounts and IPs.

Subtly charming pop culture geek. Amateur analyst. Freelance tv buff. Coffee lover